11
Key Facts
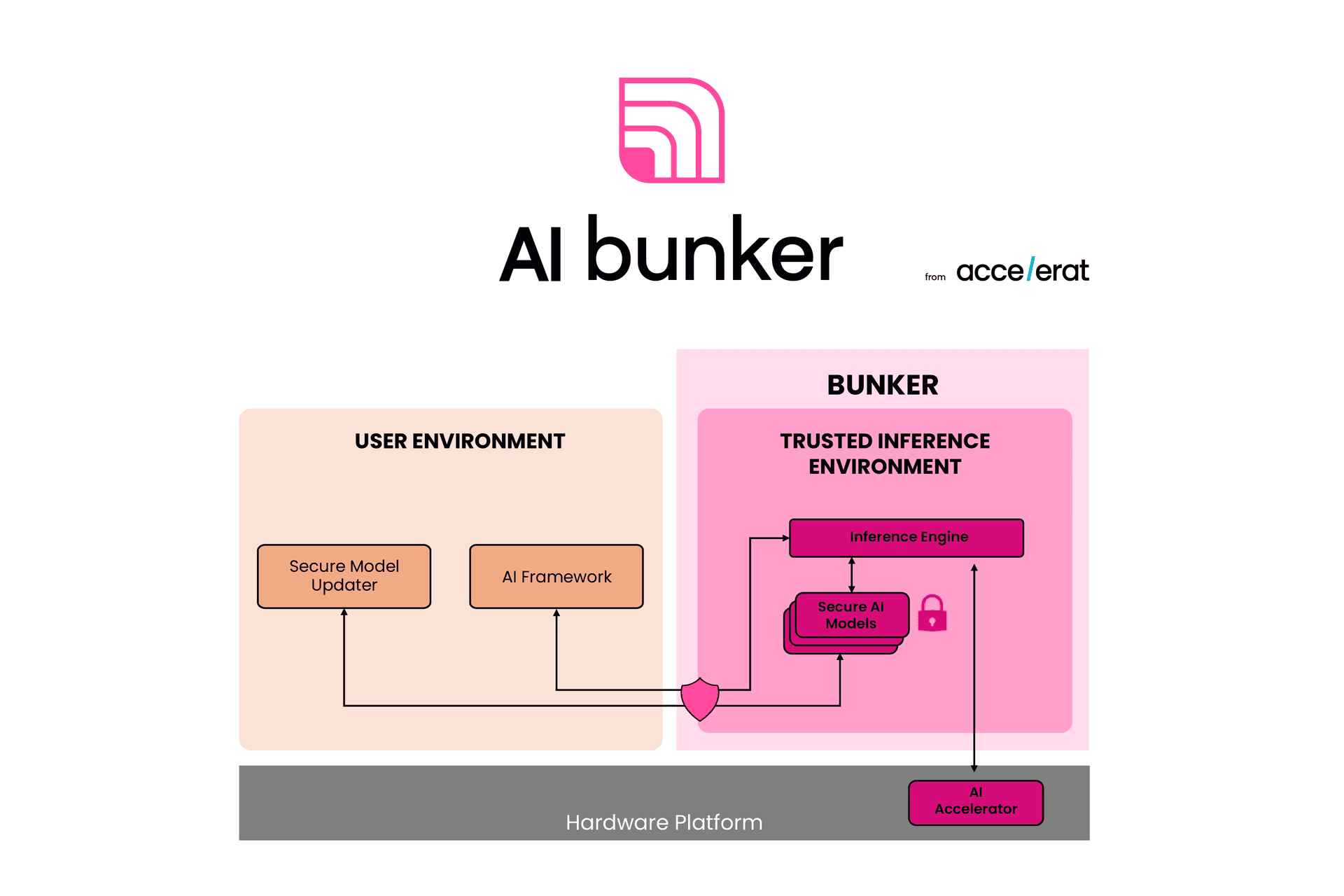
- Protection of AI Models from theft and unauthorised access
- Seamless model invocation with standard AI workflows
- Real-time inference performance
Categories
Software for Software Design Methods and Tools for Secure Embedded Systems Other Tools and Software Embedded Linux Secure Embedded Operating Systems Virtualization Software, Hypervisors Other Software for the IoT Embedded Software for Data Security Artificial Intelligence
Product information
Embedded devices increasingly rely on AI models to perform disparate tasks. Companies need to spend a lot of effort, time, and money to build AI models, such as deep neural networks, due to a long process that includes several onerous design and development phases. AI models are however susceptible to theft, tampering, and unauthorized access due to the vulnerabilities of the hardware and software environments. Concerning theft, when no proper countermeasurs are in place, attackers could steal intellectual property that required enormous investments to be generated.
Protecting the AI models on such devices while maintaining a seamless inference workflow is hence a major challenge.
Product Expert

Download product information

